
Computers and Technology, 24.02.2021 19:50 janyiareese12
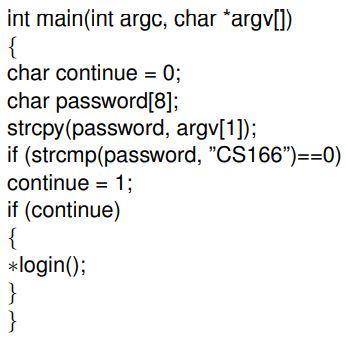
Consider the following piece of C code (in attachment):
In the above code, ∗login() is a pointer to the function login()
(In C, one can declare pointers to functions which means that the
call to the function is actually a memory address that indicates
where the executable code of the function lies). (1) Is this
code vulnerable to a buffer-overflow attack with reference to the
variables password[] and continue? If yes, describe how an attacker
can achieve this and give an ideal ordering of the memory cells
(assume that the memory addresses increase from left to right)
that correspond the variables password[] and continue of the code
so that this attack can be avoided. (2) To fix the problem, a security
expert suggests to remove the variable continue and simply use
the comparison for login. Does this fix the vulnerability? What
kind of new buffer overflow attack can be achieved in a multiuser
system where the login() function is shared by a lot of users (both
malicious and and nonmalicious) and many users can try to log
in at the same time? Assume for this question only (regardless
of real systems’ behavior) that the pointer is on the stack rather
than in the data segment, or a shared memory segment. (3) What
is the existing vulnerability when login() is not a pointer to the
function code but terminates with a return() command? Note that
the function strcpy does not check an array’s length.

Answers: 3


Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 10:00, fnaflover8505
Businesses allocate resources for their best and most productive uses. the more a resource, the more costly it will be. a manufacturer that requires scarce and costly resources is likely to charge for its products.
Answers: 2

Computers and Technology, 23.06.2019 10:00, serenityharmon1
Hey i just logged on and one of the moderators deleted a bunch of my answers to questions, even though the answers were right and the people it doesn't make sense but if anyone wants to talk about anything just message me lol (this is super random lol)
Answers: 1

Computers and Technology, 23.06.2019 23:30, huangjianhe135
The keyboard usually has six rows of keys. which of the following is not one of the key group categories? letter keys number keys control keys graphic keys
Answers: 1

Computers and Technology, 24.06.2019 00:30, Auttyrain3929
Afiling system in which an intermediary source of reference, such as a file card, must be consulted to locate specific files is called a(n) system. a. shelf filing b. direct filing c. indirect filing d. shingling
Answers: 1
You know the right answer?
Consider the following piece of C code (in attachment):
In the above code, ∗login() is a pointer to...
Questions in other subjects:

Mathematics, 29.10.2020 01:00

Chemistry, 29.10.2020 01:00


Social Studies, 29.10.2020 01:00

Mathematics, 29.10.2020 01:00


Mathematics, 29.10.2020 01:00

Mathematics, 29.10.2020 01:00


Mathematics, 29.10.2020 01:00



