
Computers and Technology, 05.02.2021 17:50 BabyDino9415
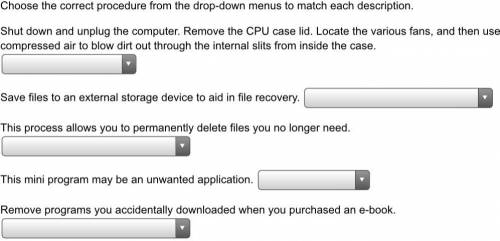
Choose the correct procedure from the drop-down menus to match each description. Shut down and unplug the computer. Remove the CPU case lid. Locate the various fans, and then use compressed air to blow dirt out through the internal slits from inside the case. Save files to an external storage device to aid in file recovery. This process allows you to permanently delete files you no longer need. This mini program may be an unwanted application. Remove programs you accidentally downloaded when you purchased an e-book. This application scans, locates, and makes needed repairs on the hard drive.


Answers: 3


Other questions on the subject: Computers and Technology

Computers and Technology, 23.06.2019 03:00, minelly1717
Your business be in google top rank. more the rank more the business leads. for best seo and digital marketing services be confident to contact you can get best seo solutions by assistance experts provide digital marketing, website development, seo expert services and social media internet seo expert services your branding solutions. seo expert services ,best seo expert services, online seo expert services,
Answers: 3


Computers and Technology, 24.06.2019 15:20, 710jonathan
Local area networks use many of the same network technologies and the internet, only on a smaller scale. devices that access lans are equipped with a network interface that contains circuitry for wireless or wired connections. devices also have a physical address, in addition to the ip addresses acquired from a dhcp server. the most popular wired technology is . the most popular wireless technology is , which can be configured as a(n) or star topology. setting up a lan and configuring its router is fairly easy. the first step is to change the standard to one that is secure. next, create a(n) that uniquely identifies the network by name. it is also important to activate wireless to prevent wireless signals from being intercepted during transmission. a limited-access network can be created for visitors to use. by activating , the router will be able to assign ip addresses to each device that joins the network. to connect to a secure lan that is protected by encryption, an encryption , or password, is required. lans can be used to access data collected by iot devices and the networks that tie these devices together. technologies such as rfid, nfc, bluetooth smart, zigbee, and z-wave offer -power links, essential for battery-powered devices that can’t expend excess amounts of energy transmitting data.
Answers: 1

Computers and Technology, 24.06.2019 18:30, HavenShort3075
These factors limit the ability to attach files to e-mail messages. location of sender recipient's ability to open file size of file type of operating system used
Answers: 1
You know the right answer?
Choose the correct procedure from the drop-down menus to match each description. Shut down and unplu...
Questions in other subjects:

Mathematics, 22.11.2020 22:40

Mathematics, 22.11.2020 22:40

Business, 22.11.2020 22:40


History, 22.11.2020 22:40

Computers and Technology, 22.11.2020 22:40

Geography, 22.11.2020 22:40



World Languages, 22.11.2020 22:40



