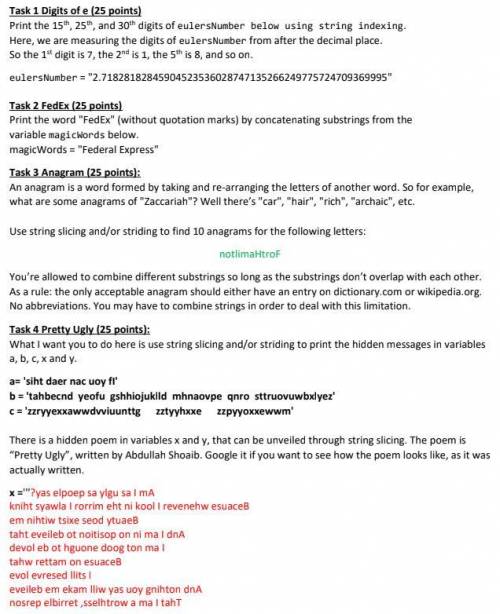
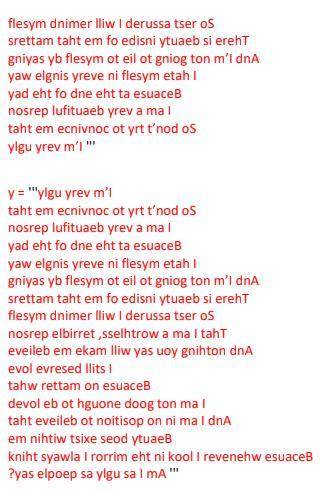
I don't understand how to do these. It's python by the way.
...

Computers and Technology, 26.11.2020 01:00 kiki4832
I don't understand how to do these. It's python by the way.

Answers: 2


Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 23:30, keviongardner
The next button in the review section shows the next available comment. next slide with no comment. previous comment. edited comment.
Answers: 1

Computers and Technology, 23.06.2019 01:30, giannav57
How do you set up a slide show to play continuously, advancing through all the slides without requiring your interaction? a. click set up slide show, and then select the loop continuously until ‘esc' and show without narration options. b. click set up slide show, and then select the loop continuously until ‘esc' and use timings, if present options. c. click set up slide show, and then select the show presenter view and use timings, if present options. d. click set up slide show, and then select the show without animation and browsed at a kiosk (full screen) options.
Answers: 3

Computers and Technology, 23.06.2019 11:00, jolleyrancher78
What are the possible consequences of computer hacking? what is computer piracy? describe some examples. what are the effects of computer piracy? what are the possible consequences of computer piracy? what is intentional virus setting? describe some examples. what are the effects of intentional virus setting? what are the possible consequences of intentional virus setting? what is invasion of privacy? describe some examples. what are the effects of invasion of privacy? what are the possible consequences of invasion of privacy? what is an acceptable use policy and what is the purpose of the acceptable use policy what is intellectual property and how can you use it?
Answers: 1

Computers and Technology, 24.06.2019 15:30, S917564
The idea that, for each pair of devices v and w, there’s a strict dichotomy between being “in range” or “out of range” is a simplified abstraction. more accurately, there’s a power decay function f (·) that specifies, for a pair of devices at distance δ, the signal strength f(δ) that they’ll be able to achieve on their wireless connection. (we’ll assume that f (δ) decreases with increasing δ.) we might want to build this into our notion of back-up sets as follows: among the k devices in the back-up set of v, there should be at least one that can be reached with very high signal strength, at least one other that can be reached with moderately high signal strength, and so forth. more concretely, we have values p1 ≥ p2 ≥ . . ≥ pk, so that if the back-up set for v consists of devices at distances d1≤d2≤≤dk, thenweshouldhavef(dj)≥pj foreachj. give an algorithm that determines whether it is possible to choose a back-up set for each device subject to this more detailed condition, still requiring that no device should appear in the back-up set of more than b other devices. again, the algorithm should output the back-up sets themselves, provided they can be found.\
Answers: 2
You know the right answer?
Questions in other subjects:



Biology, 04.08.2019 01:30









