
Computers and Technology, 27.07.2020 14:01 lbelle
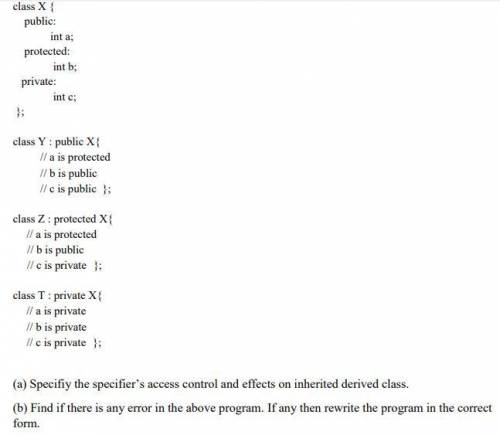
1. When creating a derived class from a base class, you can use different access specifiers to inherit the data members of the base class. The specifiers protect the members of the base class from the derived classes. The specifiers may be private, public or protected. Now, consider the following program of access specifiers with inheritance and answer the following questions:

Answers: 2


Other questions on the subject: Computers and Technology

Computers and Technology, 22.06.2019 10:10, joanasprinkman2262
3. bob is arguing that if you use output feedback (ofb) mode twice in a row to encrypt a long message, m, using the same key each time, it will be more secure. explain why bob is wrong, no matter what encryption algorithm he is using for block encryption (15 points).
Answers: 3


Computers and Technology, 22.06.2019 21:30, Nathaliasmiles
The graph shows median weekly earnings for full-time workers according to education level. which can you not conclude?
Answers: 2

Computers and Technology, 23.06.2019 15:00, victordhernandez01
Jake really works well with numbers and is skilled with computers but doesn't work well with others. which of the jobs discussed in this unit might be best for jake? why?
Answers: 3
You know the right answer?
1. When creating a derived class from a base class, you can use different access specifiers to inher...
Questions in other subjects:

Social Studies, 04.03.2021 03:00


Mathematics, 04.03.2021 03:00


Mathematics, 04.03.2021 03:00


Mathematics, 04.03.2021 03:00

Mathematics, 04.03.2021 03:00

English, 04.03.2021 03:00




