
Computers and Technology, 01.04.2020 03:14 deisyy101
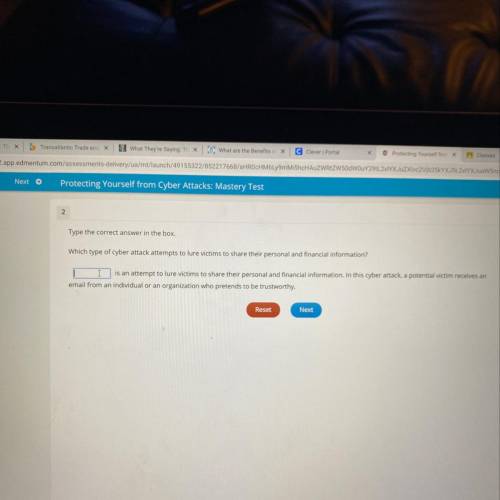
Which type of cyber attack attempts to lure victims to share their personal and financial information?

Answers: 3


Other questions on the subject: Computers and Technology


Computers and Technology, 22.06.2019 16:20, Aleja9
It policy compliance and emerging technologies respond to the following: propose at least three control measures that organizations need to put in place to ensure that they remain complaint with emerging technologies and in a continually changing it environment. examine the correlation of effective configuration management and change control procedures to remain compliant with emerging technologies and it security changes.
Answers: 2

Computers and Technology, 22.06.2019 21:00, mazolethrin9632
Which of these is most responsible for differences between the twentieth century to the twenty-first century?
Answers: 2

Computers and Technology, 23.06.2019 04:20, milkshakegrande101
4. a1. vince owns a television repair shop that is insured undera commercial package policy. the policy includes thebuilding and personal property coverage form and thecauses-of-loss broad form. the declarations page indicatesthat coverage applies to both the building and the namedinsured's business property. explain whether or not thefollowing losses would be covered under his policy. a. a fire occurs on the premises, and the building isbadly damaged. b. a burglar steals some money and securities from anunlocked safe. c. a business computer is damaged by vandals whobreak into the shop after business hours. d. a tornado touches down near the store. several tel-evision sets of customers in the shop for repair aredamaged in the storm. til
Answers: 2
You know the right answer?
Which type of cyber attack attempts to lure victims to share their personal and financial informatio...
Questions in other subjects:










English, 06.03.2020 15:53



