This problem performs elliptic curve encryption/decryption using the scheme out-
lined in secti...

Computers and Technology, 02.01.2020 20:31 himatasy
This problem performs elliptic curve encryption/decryption using the scheme out-
lined in section 10.4. the cryptosystem parameters are e11(1,6) and g = (2,7). b's
secret key is nb = 3. (hint: note the relationship of this system to the one discussed in
the previous question (10.14)]
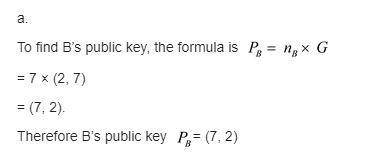
a. find b's public key pb.
b. a wishes to encrypt the message pm = (10,9) and chooses the random value
k = 4. determine the ciphertext cm.
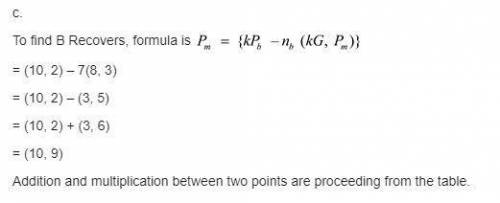
c. show the calculation by which в recovers pm from cm.
(10.> for e11(1,6) consider the point g=(2,7). compute the multiple of g from 2g through 13g.)

Answers: 1


Other questions on the subject: Computers and Technology

Computers and Technology, 24.06.2019 03:00, SiegeHatake4534
Will do anything for brainlest so can you guys me out i will try my best to you out
Answers: 1

Computers and Technology, 24.06.2019 18:20, mshepherdmiller
Acommon algorithm for converting a decimal number to binary is to repeatedly divide the decimal number by 2 and save the remainder. this division is continued until the result is zero. then, each of the remainders that have been saved are used to construct the binary number. write a recursive java method that implements this algorithm. it will accept a value of int and return a string with the appropriate binary character representation of the decimal number. my code: public class lab16{public string converttobinary(int input){int a; if(input > 0){a = input % 2; return (converttobinary(input / 2) + "" +a); } return ""; } }
Answers: 1


Computers and Technology, 25.06.2019 02:30, Nismo3501037
What are the charges for invasion of privacy on computers
Answers: 1
You know the right answer?
Questions in other subjects:






Mathematics, 02.09.2020 20:01




 "(b) The ciphertext is "
"(b) The ciphertext is " "(c) Between the two points, addition as well as multiplication are proceeding.
"(c) Between the two points, addition as well as multiplication are proceeding.