product materials a, b, c, d and e which sells

Computers and Technology, 25.08.2019 12:30 mak6156
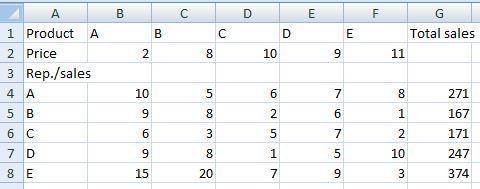
Kofi pharmaceutical company has the following
product materials a, b, c, d and e which sells
for $2 $8 $ 10 $9 and 11 respectively
there are five salesman working for the company
and the following statement gives the sales report
for each product item,
first salesman sold, 10, 5, 6, 7 and 8 respectively
second salesman sold ; 9, 8, 2, 6 and i respectively
third salesman sold, 6, 3,5,7 and 2 respectively
fourth salesman sold, 9, 8, 1,5 and to respectively
firth salesman sold, 15, 20, 7, 9 and 3 respectively
represent
the
information
above
in
microsoft excel

Answers: 2


Other questions on the subject: Computers and Technology

Computers and Technology, 23.06.2019 22:00, elijah1090
Technician a says engine assemblies can be mounted longitudinally in a chassis. technician b says engine assemblies can be mounted transversely in a chassis. who is correct?
Answers: 2

Computers and Technology, 24.06.2019 17:00, rosepetals2938
Carlos, an algebra teacher, is creating a series of powerpoint presentations to use during class lectures. after writing, formatting, and stylizing the first presentation, he would like to begin writing the next presentation. he plans to insert all-new content, but he wants to have the same formatting and style as in the first one. what would be the most efficient way for carlos to begin creating the new presentation? going under the file tab and opening the first presentation, deleting all content from each page, and adding new content going under the file tab and clicking on new in the left pane, then choosing new from existing going under the design tab and clicking on themes, then selecting the theme that was used for the first template going under the design tab and opening the template that was created for the first presentation
Answers: 2

Computers and Technology, 24.06.2019 21:30, keelynnbarrier
Computer security/cybersecurity1) each of the following code fragments contains a number of security vulnerabilities. for each fragment, identify these security vulnerabilities and, for each vulnerability, discuss at least one way that it could be improved. note that in your discussion of how each vulnerability could be improved, you do not need to re-write a new version of the program in c; simply discuss your solution, either in pseudocode or in 1-2 sentences. a) /* file descriptor leak */#include #include int main(int argc, char *argv[]){ char *filepath = argv[0]; char *shellpath = argv[1]; file *passwords; passwords = fopen(filepath, "r"); /* read the password and do something with it */ /* . . */ /* fork and execute alternative shell */ execl(shellpath, "shell", null); }b)#include /* assume the following function is written for an electronic storefront. the user will enter the id of the item to be ordered, as well as the quantity of units that they would like to purchase. the program will then lookup the price for the price for the item using a predefined function, and return the total cost of the order.*/int gettotalcost(){ char itemid[9]; int price, unitsordered, cost; printf(" enter the 9-digit id of the item to be ordered: "); scanf("%s", & itemid); /* lookup the price according to the itemid */ price = getpricebyid(itemid); printf(" enter the quantity of units to be ordered: "); scanf("%d", & unitsordered); cost = price * unitsordered; return cost; }c)#include /* the following function is intended to return a user's full name by concatenating the user's first and last name into a single string and then returning that string. */char *getfullname(char *firstname, char *lastname, int max_len){ char fullname[max_len]; strcpy(fullname, firstname); strcat(fullname, " "); strcat(fullname, lastname); return fullname; }d)#include /* the following code snippet runs through the list of cli arguments entered and displays them to the console. */int main(int argc, char *argv[]){ int i; printf("you've entered the following arguments: "); for(i = 0; i < argc; i++){ print(argv[i]); printf("\n"); } /* */}
Answers: 2

Computers and Technology, 25.06.2019 08:10, AgarioEdit
Is a philosophy and a software and system development methodology that focuses on the development, use, and reuse of small, self-contained blocks of codes to meet the software needs of an organization. joint application designextreme programmingrapid application developmentservice-oriented architecture
Answers: 1
You know the right answer?
Kofi pharmaceutical company has the following
product materials a, b, c, d and e which sells
product materials a, b, c, d and e which sells
Questions in other subjects:


History, 23.08.2019 18:30

Biology, 23.08.2019 18:30


Mathematics, 23.08.2019 18:30

History, 23.08.2019 18:30